How AI Is Making Phishing Attacks Nearly Undetectable (And What to Do About It)
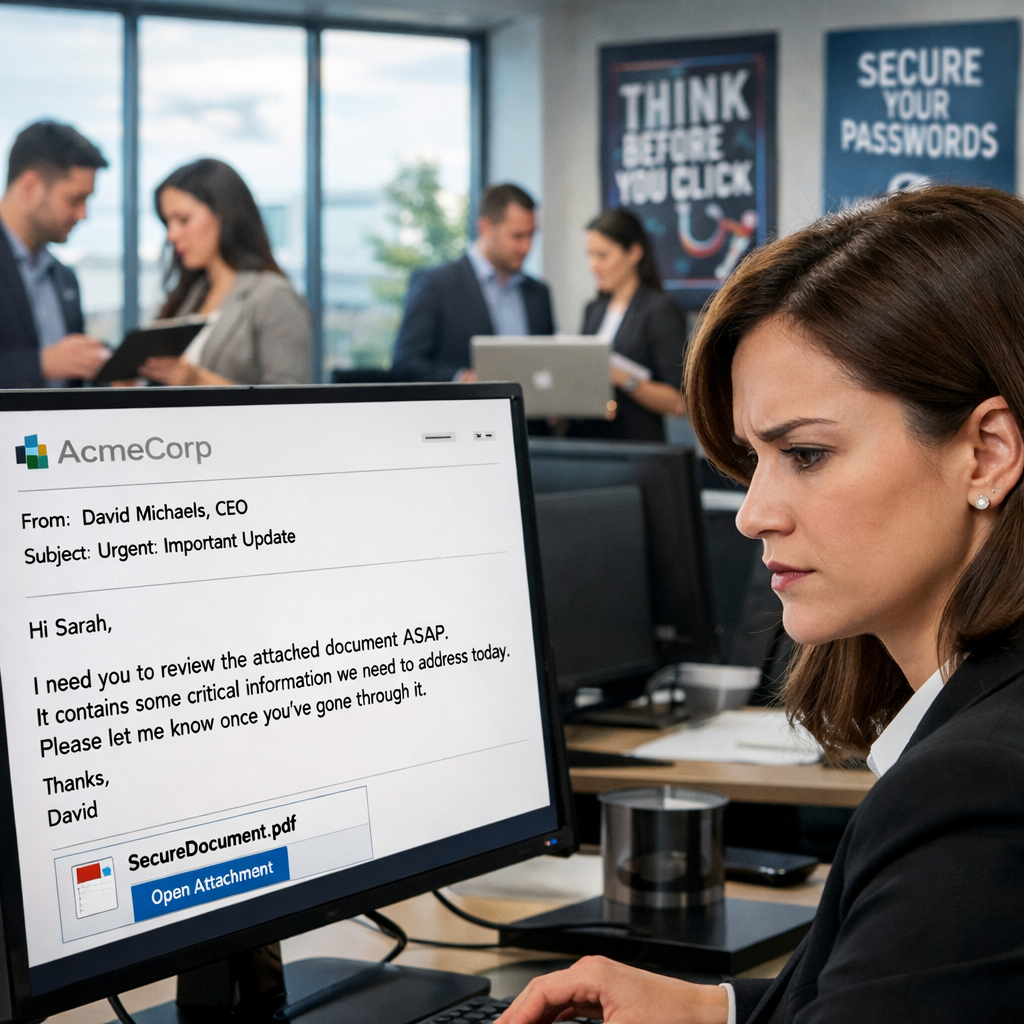
An employee opens their inbox and sees a message from the company's CFO. The tone sounds right. Direct, a little pressed for time. The email signature is formatted correctly. The request is routine: help process an invoice before end of day.
The payment goes through. The CFO never sent the email.
This isn't a story about a careless employee. It's a story about an attack so well-crafted that most people, including experienced professionals, would have responded the same way.

Why Phishing Training Is Becoming Outdated
For years, phishing emails were easy to spot. Broken English. Odd formatting. A generic "Dear Customer" greeting. Security awareness programs trained employees to catch exactly these signals, and it worked, to a point.
That approach may now be doing more harm than good. Employees who have been trained to look for sloppy writing may feel a false sense of confidence when a message looks clean and professional. And today, AI can generate clean and professional content on demand, in seconds, at scale, in any language.
The old warning signs haven't disappeared entirely, but they're no longer reliable filters. Attackers using AI tools have simply engineered them out of existence.
What AI Has Actually Changed About These Attacks
AI is changing phishing attacks across several dimensions:
- Personalization at scale: Attackers can scrape LinkedIn, company websites, press releases, and social media to build a detailed profile of your organization. A phishing email referencing a real colleague, a recent project, or a specific vendor is far more convincing than a generic one. This used to take hours of manual work per target. Now it takes seconds.
- Voice impersonation: This is the part most organizations aren't prepared for. Using a few minutes of audio pulled from a public interview, a conference recording, or a company video, attackers can recreate a convincing imitation of an executive's voice. Employees receiving a phone call from someone who sounds like their CEO asking for a wire transfer are operating in a territory their training never covered.
- Automated iteration: AI allows attackers to test variations of phishing messages and optimize based on response rates, essentially A/B testing their fraud campaigns. This is how sophisticated marketing works. Criminals are now doing the same.
The result is that attackers can now run operations that would have previously required a large, skilled team. It now takes a single person and a handful of AI tools.

The Employees Most at Risk
Phishing attacks don't hit everyone equally. Attackers concentrate their effort where the payoff is highest. That means employees who handle financial transactions, manage vendor relationships, hold administrative system access, or work directly with executives are the most common targets.
Even the CFO may receive a convincing message impersonating IT support asking for their credentials. No title protects someone from a well-crafted attack, and AI-assisted attacks can be tailored to any role.
How to Defend Against These Attacks
The honest answer is that no single defense is enough. The organizations that fare best layer several approaches together:
- Verify through a separate channel: Any request involving a financial transaction, a password reset, or a change to payment details should be confirmed via a second, independent channel: a direct phone call to a known number, or an internal message on a platform the attacker can't access. This one procedure stops a significant share of attacks cold, regardless of how convincing the original message was.
- Update your training to reflect modern attacks: Security awareness programs that still focus primarily on spotting typos are teaching the wrong lesson. Training should reflect how phishing attacks are evolving. This includes recognizing personalized messages and understanding that unusual requests should always be verified, even when they appear to come from someone familiar.
- Implement multi-factor authentication everywhere: MFA doesn't prevent employees from being deceived, but it contains the damage. If credentials are stolen through phishing, an attacker still can't access systems without the second factor. This is one of the highest-value security investments an organization can make.
- Deploy email security tools that analyze behavior, not just content: Traditional filters look for known bad patterns. Modern platforms learn what normal communication looks like within your organization and flag anomalies. An email that mimics the CFO's writing style but originates from an unusual server, for instance. These tools aren't perfect, but they catch attacks that content-based filters miss entirely.
- Audit your public digital footprint: Attackers build targeting profiles from publicly available information. Periodically review what your company website, employee LinkedIn profiles, and press releases reveal about your internal structure, team names, vendors, and ongoing projects. Reducing unnecessary exposure raises the effort required to mount a targeted attack.
This last point is easy to overlook but often significant. A detailed org chart, a blog post naming your logistics vendors, or a LinkedIn profile listing internal project names all give attackers a head start.
Building a Culture Where People Speak Up
One of the most underrated defenses against phishing is psychological: employees who feel safe questioning a suspicious request, and comfortable reporting when something doesn't seem right.
Attacks often succeed not because an employee was careless, but because they were afraid to slow down an apparent request from a senior leader. A workplace culture where questioning an unusual request, even one that appears to come from the top, is not just acceptable but expected, removes a key lever that attackers rely on.
Security awareness should be ongoing. Sharing examples of real phishing attempts your organization receives keeps the threat visible and concrete. Recognizing employees who catch and report suspicious messages reinforces the right behaviors.

Why Phishing Defense Needs a New Approach
AI has lowered the barrier to creating convincing phishing attacks so dramatically that the threat landscape has changed in just a few short years. Emails that once required skill, time, and strong language skills to produce can now be generated by anyone, personalized to a specific target, and refined in seconds.
The organizations best positioned to defend themselves are those that stop treating phishing as a training problem and start treating it as a process problem. The right verification procedures, applied consistently, stop most attacks regardless of how convincing they appear.
The message that looks perfectly fine is no longer a reassuring sign. It might be exactly the one to watch out for.
Protecting your organization from AI-powered phishing starts with the right security strategy. Pulse Technology's cybersecurity team can help you assess your current defenses and close the gaps. Contact us today.