Cybersecurity Solutions

Avoid Cyber Threats Without The Frustration
In a world where over half a million new malware threats emerge daily, protecting your business is more crucial than ever. The fear of cyber attacks can weigh heavily on decision-makers, but with Pulse Technology, you can turn that fear into confidence. Our comprehensive cybersecurity services go beyond the basics to offer robust layers of protection for your valuable data and sensitive information. We don’t just implement solutions; we empower your team with cybersecurity training, equipping them to recognize and respond to threats effectively. With Pulse by your side, you can focus on what truly matters - growing your business - knowing that your cybersecurity is in expert hands.
QUICK LINKS
"They also proactively plan for your company's future needs, providing affordable and realistic options..."
Dark Web Scanning
& Vulnerability Management
Find weaknesses through simulated attacks while identifying and fixing them to minimize attack points and strengthen your overall security.
Penetration Testing
Penetration testing simulates cyberattacks to identify vulnerabilities, helping organizations improve security and protect their digital infrastructure.
Total Security
Unified Threat Management (UTM) based firewall solution including cloud sandboxing, AI-powered anti-malware protection, DNS filtering, and network and endpoint threat correlation protects your infrastructure from outside threats.
Emergency Response Planning
Creating a cybersecurity emergency response plan is crucial for organizations to effectively respond to and mitigate cyber incidents. A well-designed plan should be regularly tested to ensure its effectiveness.
Security Information & Event Management (SIEM)
Our SIEM solution is backed by a 24x7 Technical Support Group (TSG) to help you meet compliances and most importantly protect your infrastructure from known and unknown threats.
Managed
Security
The number of cyber-attacks is at an all-time high and cyber criminals are focusing on small to midsize businesses. Pulse Technology can offer a comprehensive suite of tools to keep your business and employees safe.
Endpoint Detection & Response (EDR)
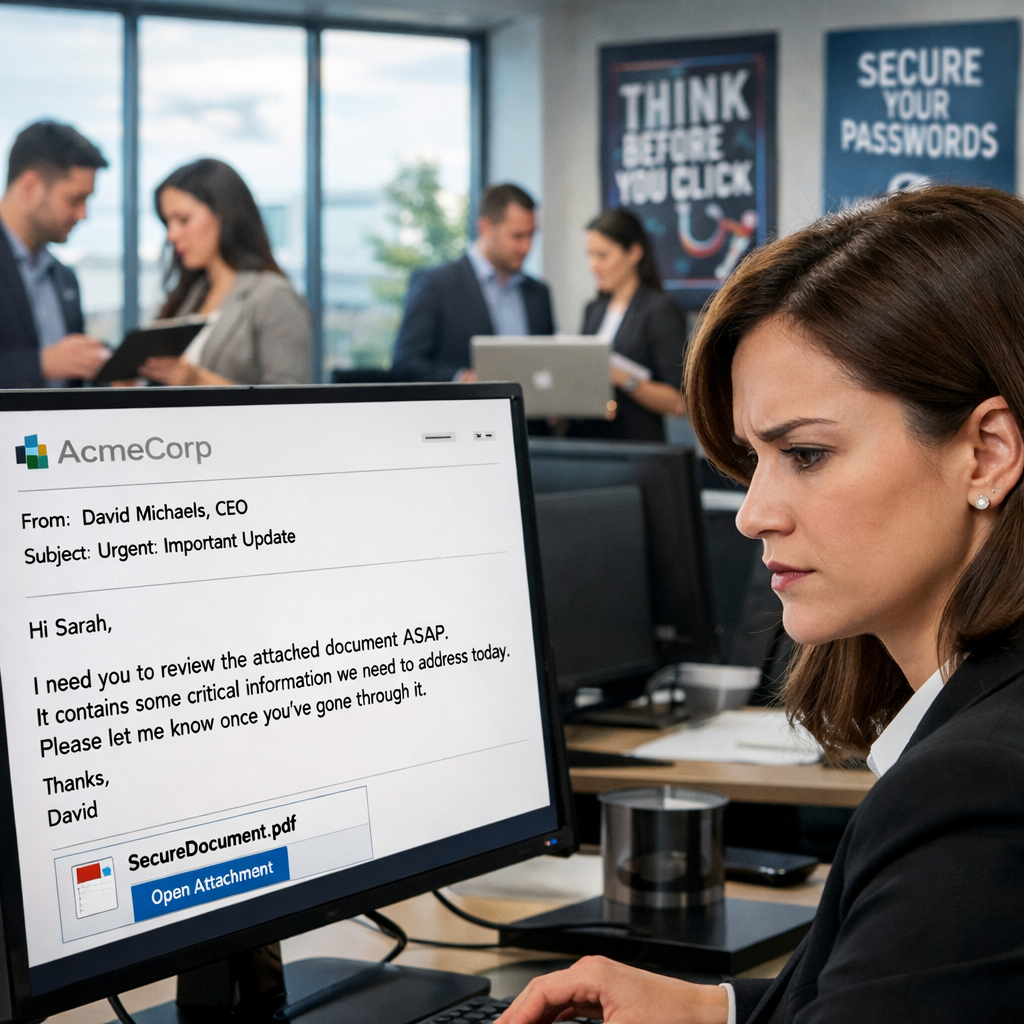
Security Awareness Training
Security awareness training educates employees about common attack vectors, such as phishing emails and social engineering techniques, and teaches them how to identify suspicious activities and potential risks.
Email Encryption, Journaling & Spam Protection
An easy-to-use email encryption platform and journaling-based retention help you meet your compliance requirements. Add on spam filtering to help secure your employees' mailboxes.
Secure Wifi & Remote Workers
Secure your employees in remote workplaces including public WIFI locations. Secure Access Service Edge (SASE) provides a modern approach to VPN connectivity and keeps all data to and from your employee’s devices encrypted.
Third-Party
Testing
Third-party assessment provides an unbiased security check. These experts evaluate your defenses and compliance, providing a fresh perspective on your cybersecurity posture.
Managed Antivirus
Comprehensive, round-the-clock protection by detecting and neutralizing malware, viruses, and other cyber threats before they can cause harm. With real-time monitoring, automatic updates, and expert management.
Risk Assessments
Evaluate potential threats and vulnerabilities within your organization's systems, processes, and assets and prioritize and implement targeted security measures.
Third-Party
Testing
Third-party assessment provides an unbiased security check. These experts evaluate your defenses and compliance, providing a fresh perspective on your cybersecurity posture.
Secure Your
Organization
and Data
Our cybersecurity experts are here to give you peace of mind.
What would happen if ransomware shut down your business today?
Cyberattacks now target small and mid-sized companies more than large enterprises. Most business owners don’t realize their systems are vulnerable until it’s too late.
Pulse Technology provides advanced cybersecurity services designed specifically for Illinois businesses, including law firms, accounting firms, and professional services companies.
✔️ 24/7 Security Operations Center
✔️ Risk and Vulnerability Assessments
✔️ Dark Web Credential Scanning
✔️ Endpoint Detection and Managed Antivirus
✔️ Phishing Simulations and Employee Security Training
✔️ Emergency Breach Response Plans
✔️ Secure Wi-Fi and Office 365 Protection
We help businesses prevent cyberattacks, reduce risk, and recover quickly — with less than 1 percent unplanned downtime per year.
between 2022 and 2023.
-
Certified Information Systems Security Professional (CISSP)
-
Certified Information Security Manager (CISM)
-
Certified Cyber Security Awareness Practitioner (CSAP)
-
CMMC Registered Practitioner
-
SANS GCIH Silver: Hacker Techniques, Exploits, and Incident Handling
-
SANS GCIA Silver: Intrusion Detection In-Depth
-
Qualified Security Assessor (QSA)
-
Certified Ethical Hacker (CEH)
-
Payment Application Qualified Security Assessor
-
GIAC Security Essentials (GSEC)