Two-Factor Authentication: What is it and Why Do You Need It?
For many people, using two-factor authentication (or, MFA, multi-factor authentication) can seem like an annoying extra step that gets in the way of our logging in and getting down to business. It’s time consuming. It requires additional efforts. And, we might wonder, do we really need to take those additional precautions?
The answer to that question is a resounding yes! We all need to take those extra steps to improve our cybersecurity. Using two-factor authentication (2FA) can make a big difference when it comes to protecting data. Yet, according to research by career placement company Zippia , only 13% of SMBs (small and medium sized businesses) require employees to use two-factor authentication when logging in. The same research shows that only 27% of government employees do so, 33% of educators, and in the telecommunications industry it’s 31% of employees who use 2FA.

The numbers improve with larger businesses, where 87% of employees are required to use two-factor authentication. But increasingly cyber criminals are targeting smaller businesses, where the track record of using 2FA is lesser. An Accenture Cybercrime Study shows that 43% of all attempted hackings are at the small business level.
The Zippia report further states that using multi-factor authentication can block more than 99% of automated cyber attacks, 76% of targeted attacks, and 96% of bulk phishing attacks. And two-factor authentication can reduce Google hack attempts by 50%. Still, less than 10% of Google accounts use 2FA.
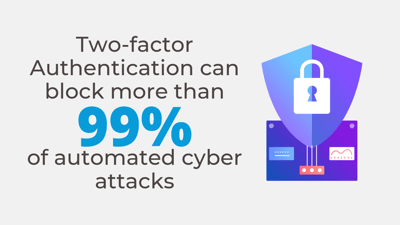
Combine those numbers with the fact that more than 80% of hacking related breaches are due to weak or stolen passwords, and it seems clear that there is a real need for two-factor or multi-factor authentication on our systems.
2FA and MFA are becoming more common in the workplace, which is a good sign. The job site Indeed encourages both employers and job seekers to safeguard their recruitment data and offers 2FA options to employer accounts. A number of the University of Chicago website offerings use 2FA, and you’ll see it increasingly in more and more locations.
What is Two Factor Authentication
You may have used 2FA, possibly without even knowing you were. When you access certain websites and you are asked to provide a cell phone number for texting a code, that’s a two-factor or mulit-factor authentication. It’s similar in principle to protecting your bank account with a PIN number.
What is the Benefit of 2FA?
If a password has been compromised, that information alone isn’t sufficient to allow a hacker access to your information, unless he/she can successfully get approval at this second level of security. We’ve all seen instances where we receive multiple “friend” requests followed by a notice from the original account holder that the account had been hacked. Multi-factor authentication will prevent that from happening.
It also provides an active, as opposed to more passive, security measure. When a 2FA notification (often although not always by cell phone) comes to a user that individual will know if he/she initiated the action, and can stop it right at that point if it came from somewhere else.
How Do You Use Two Factor Authentication?
The process for using 2FA is fairly straightforward. As a user, you log into the site with user name and password. Assuming that checks out, you are then asked how you would like to receive notification sent to your email, cell phone or other device. When you receive the unique code, usually a combination of numbers, you confirm your identify by approving the additional authentication within a set time frame.
In most instances, going through the 2FA process is only an additional minute or two at the most and it is time well spent. Even strong passwords are vulnerable to attack, and most people do not use strong passwords. In fact, one survey shows that 30% of Internet users have experienced a data breach due to a weak password.
Two-thirds of Americans use the same password across multiple accounts, and, perhaps unbelievably, the most common password used is “123456.”
With that said, it is very important that all of your accounts, business and personal, carry this additional security measure.
The 2FA is an important part of security protection – but it is just a single step. It’s important to be sure that your infrastructure is protected against cyber threats and your team is aware of the importance of security. As we have said previously, a network is only as secure as its weakest link. If you are looking to be certain that your network is secure, or if you have questions about today’s topic or anything else related to IT or technology, please contact us for more information or give us a call at (888) 357-4277. We look forward to hearing from you!