Personal Devices are a security risk to your network
Pulse Technology
·
2 minute read
Bringing your own devices (BYOD) into school or work is now the norm. However, this practice comes with security concerns for both individuals and organizations. Let's discuss these concerns and what you can do to mitigate them.
Organization Concerns
- Security - BYOD can introduce security risks, as personal devices may not be as well-protected as company-owned devices. This could lead to data breaches, malware infections, and other security problems.
- Compliance - Businesses and organizations may be subject to regulations that require them to protect certain types of data. BYOD can make it difficult to ensure that all data is compliant, as personal devices may not be subject to the same security controls as company-owned devices.
What you can do about it
- Start with a risk assessment - Before implementing a bring your own device policy, businesses and organizations should conduct a risk assessment to identify the potential risks associated with BYOD. This will help them to develop a policy that mitigates these risks.
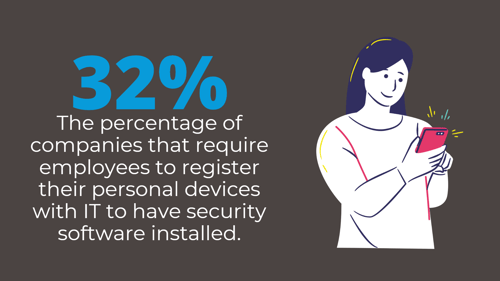
- Create a clear policy - The bring your own device policy should be a part of your cybersecurity policy. It needs to be clear and concise, and it should address all of the relevant issues, such as data security, compliance, and support.
- Educate employees - Employees need to be educated about the BYOD policy and the risks associated with BYOD. This will help them to use their personal devices safely and securely.
- Monitor compliance - Businesses and organizations need to monitor compliance with the BYOD policy. This will help to ensure that the policy is being followed and that the risks associated with BYOD are being mitigated.
Individual Concerns
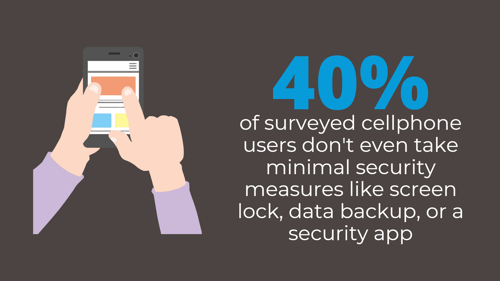
- Unsecure networks - If a personal device is connected to an unsecured network, such as a public Wi-Fi network, it could be vulnerable to attack. Attackers could intercept data that is being transmitted over the network, such as passwords or credit card numbers.
- Unpatched software - Personal devices are often not kept up to date with the latest security patches. This can leave them vulnerable to attack while on unsecured networks.
What you can do about it
- Encrypt their devices with VPN - this encrypts your internet traffic and routes it through a remote server. This makes it appear as if you are connecting to the internet from the location of the VPN server, rather than from your actual location.
- Install security software - This software can help to protect the device from malware infection.
- Only connect to secure networks - When possible, individuals should only connect their personal devices to secure networks, such as those that use a password or certificate to authenticate users.
- Keep their software up to date - Individuals should regularly check for and install security patches for their devices.
Secure your organization’s data from outside threats.